Privilege Escalation Flaw: Manage Engine Op Manager
Vendor: Zoho Corporation Pvt. Ltd.
Product web page: https://www.manageengine.com
Affected version: 12.3
Summary: OpManager offers comprehensive network monitoring capabilities that help you monitor network performance, detect network faults in real time, troubleshoot errors, and prevent downtime. Being a powerful network monitor, it supports multi-vendor IT environments and can scale to fit your network, regardless of its size. Monitor your devices and network to gain complete visibility and control over your entire network infrastructure. It allows you to monitor critical performance metrics like availability, CPU, disk space, and memory utilization across physical and virtual servers.
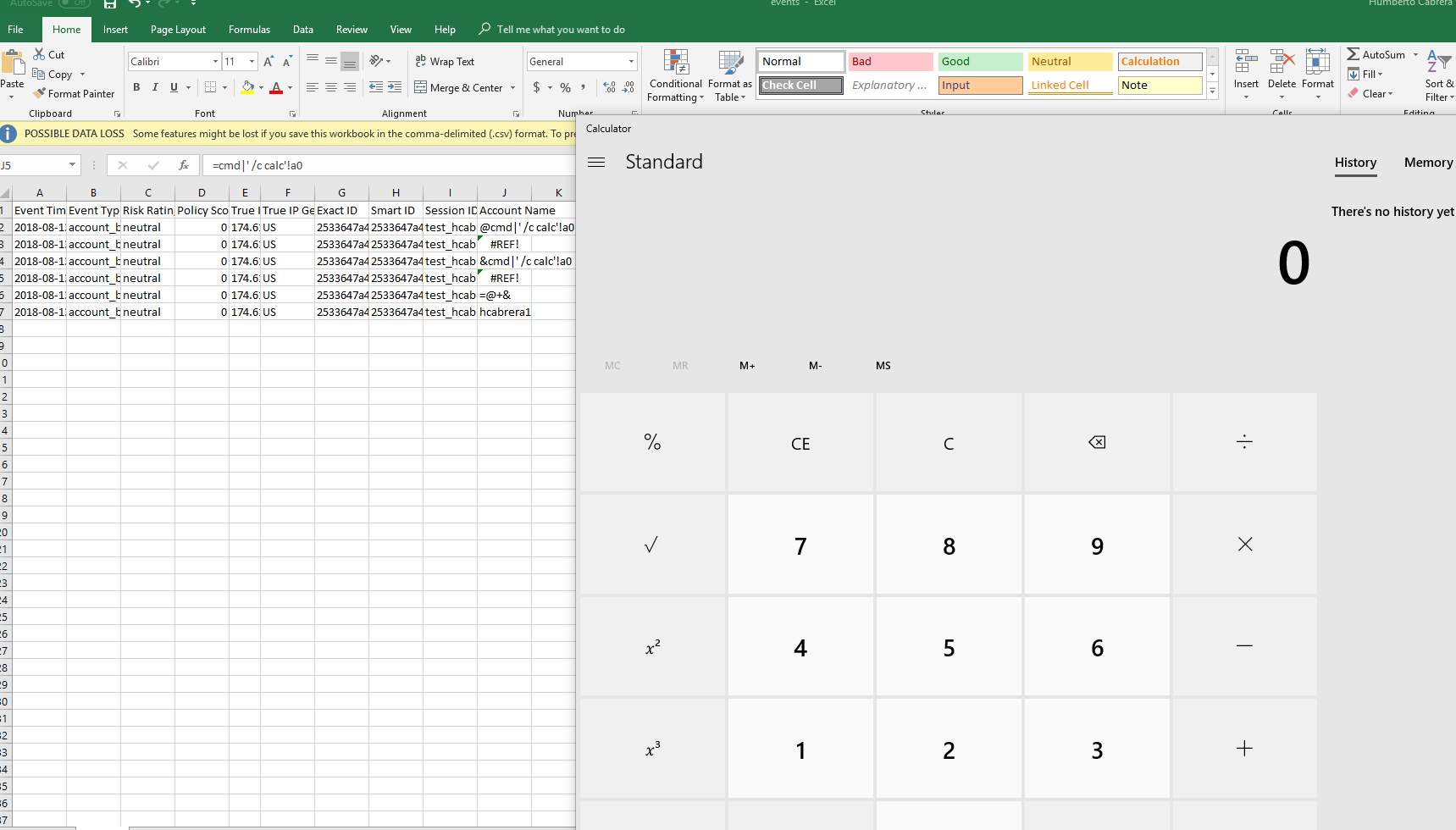
Description: The OpManager Monitoring service suffers from a weak permissions issue in which an attacker can replace the service binary with a binary of their choice. This service runs as Localsystem thus allowing for a privilege escalation vector.
Tested on: Microsoft Windows 7 x64
Advisory ID: ZSL-2019-5504
Advisory URL: https://www.zeroscience.mk/en/vulnerabilities/ZSL-2019-5504.php
14.01.2019
--
C:\Users\User>sc qc opmanager
[SC] QueryServiceConfig SUCCESS
SERVICE_NAME: opmanager
TYPE: 10 WIN32_OWN_PROCESS
START_TYPE: 2 AUTO_START
ERROR_CONTROL: 1 NORMAL
BINARY_PATH_NAME: C:\ManageEngine\OpManager\bin\wrapper.exe -s C:\ManageEngine\OpManager\conf\wrapper.conf
LOAD_ORDER_GROUP:
TAG: 0
DISPLAY_NAME: ManageEngine OpManager
DEPENDENCIES:
SERVICE_START_NAME : LocalSystem
C:\ManageEngine\OpManager\bin>icacls wrapper.exe
wrapper.exe BUILTIN\Administrators:(I)(F)
NT AUTHORITY\SYSTEM:(I)(F)
BUILTIN\Users:(I)(RX)
NT AUTHORITY\Authenticated Users:(I)(M) <==- Weak Permissions allowing the modification of the service binary
—
Humberto Cabrera
Senior Security Consultant
Prescient Security